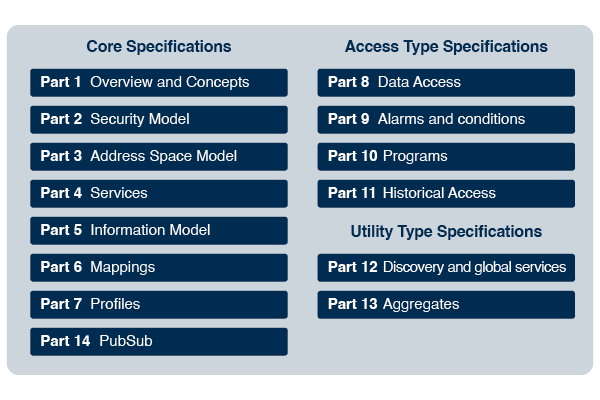
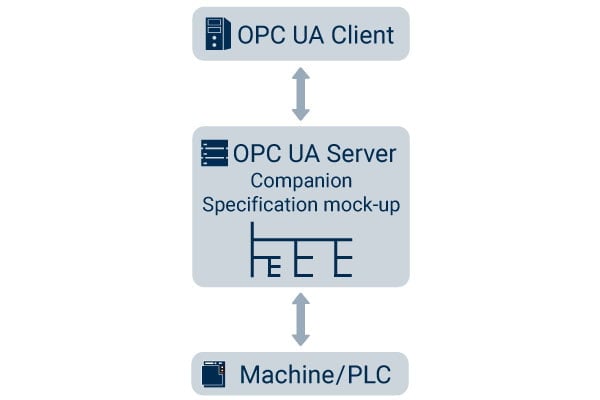
UA Part 6: Mappings - 6 Message SecurityProtocols
Por um escritor misterioso
Descrição
world Interfaces play a crucial role in today's networked
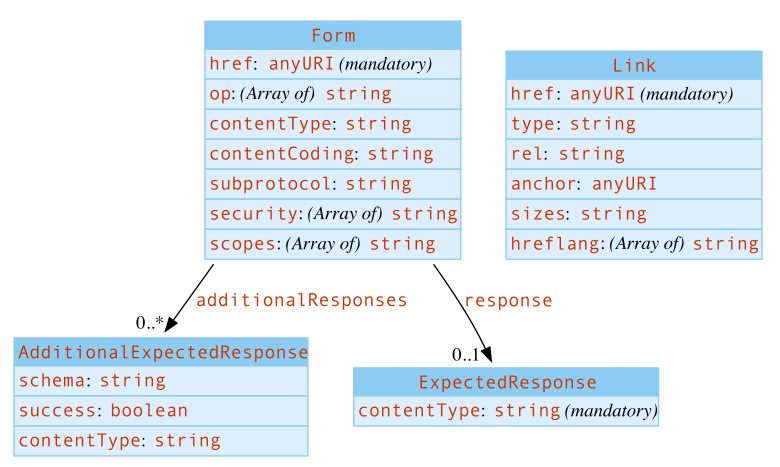
Web of Things (WoT) Thing Description 1.1

OPC Unified Architecture

What is driving the adoption of Chinese surveillance technology in Africa? - DFRLab
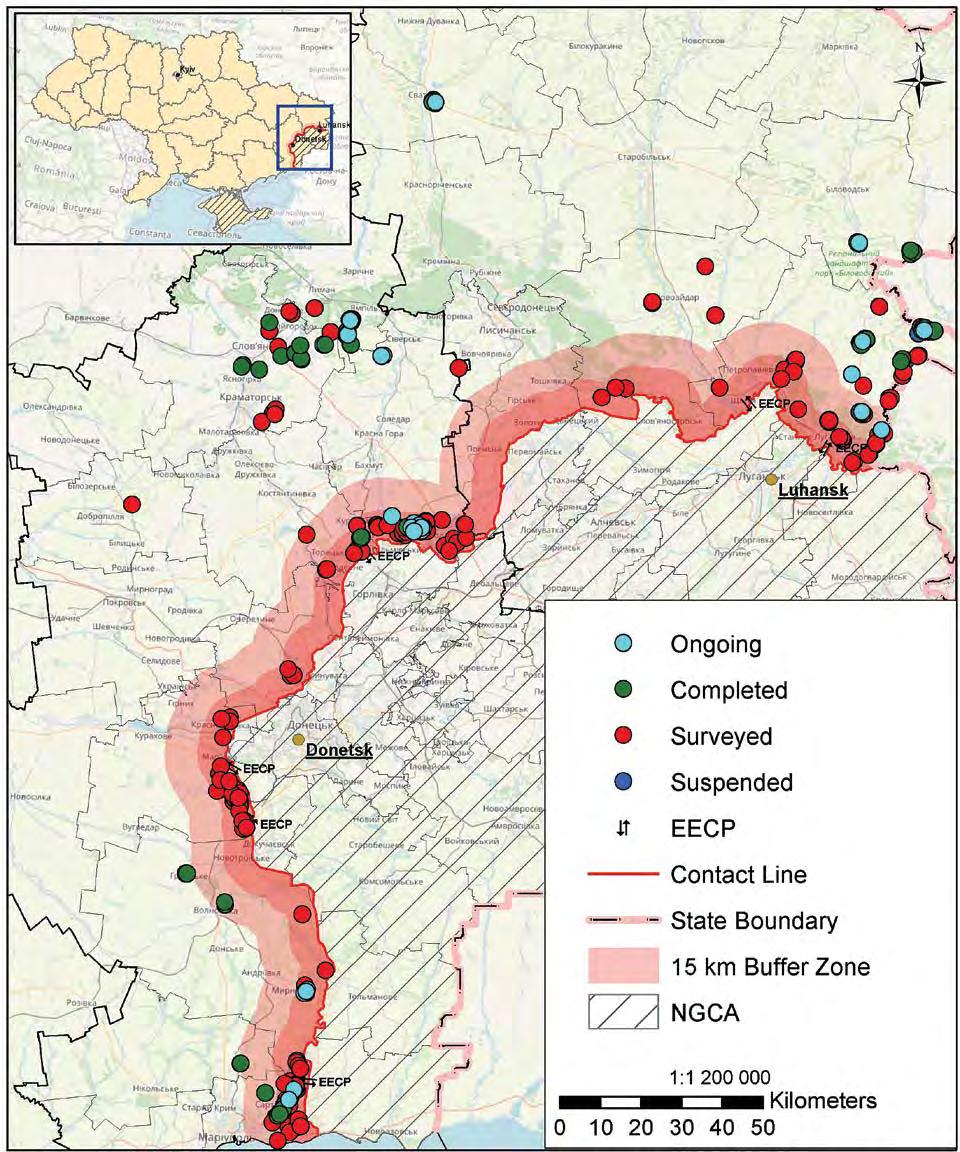
The Journal of Conventional Weapons Destruction Issue 25.1 by The Center for International Stabilization and Recovery - Issuu

4 OPC Security architecture · OPC UA
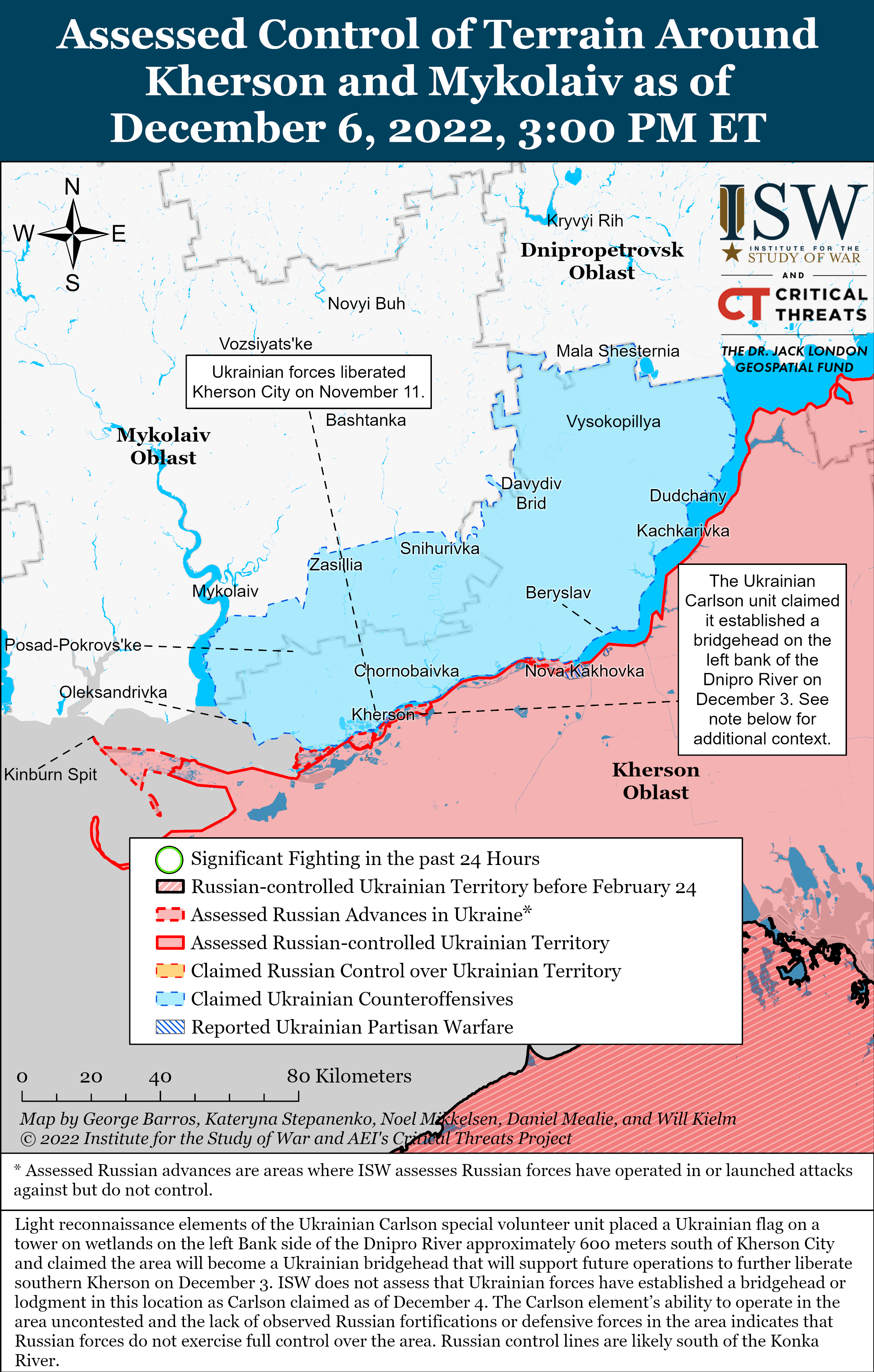
Russian Offensive Campaign Assessment, December 10
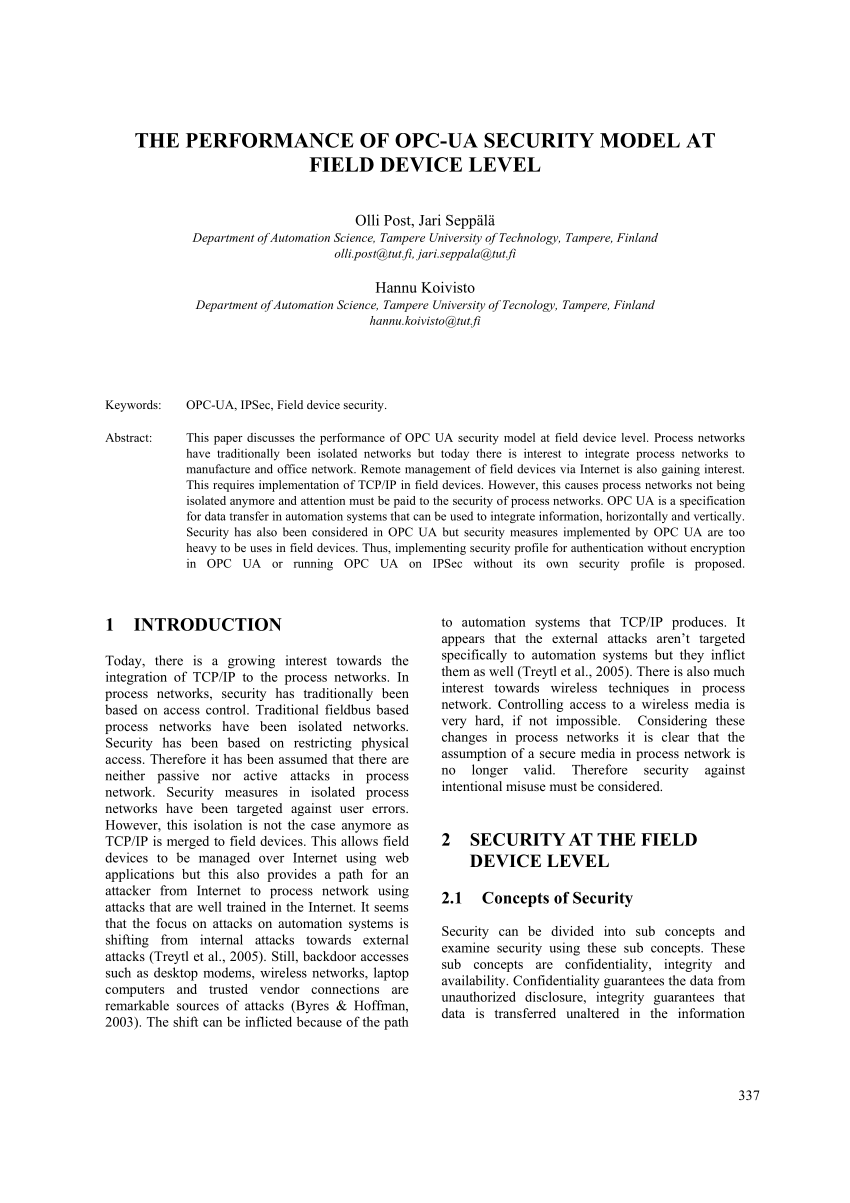
PDF) The Performance of OPC-UA Security Model at Field Device Level.
world Interfaces play a crucial role in today's networked

Gaining trust by tracing security protocols - ScienceDirect

Semantic Attribute-Based Access Control: A review on current status and future perspectives - ScienceDirect
de
por adulto (o preço varia de acordo com o tamanho do grupo)