IoT Botnets: Advanced Evasion Tactics and Analysis – Part 2
Por um escritor misterioso
Descrição
Nozomi Networks Labs analyzes new modification techniques malware authors use to evade detection and analysis tools.
JSAN, Free Full-Text

IoT Botnets: Advanced Evasion Tactics and Analysis – Part 2

Groups & tactics — Elastic Security Labs
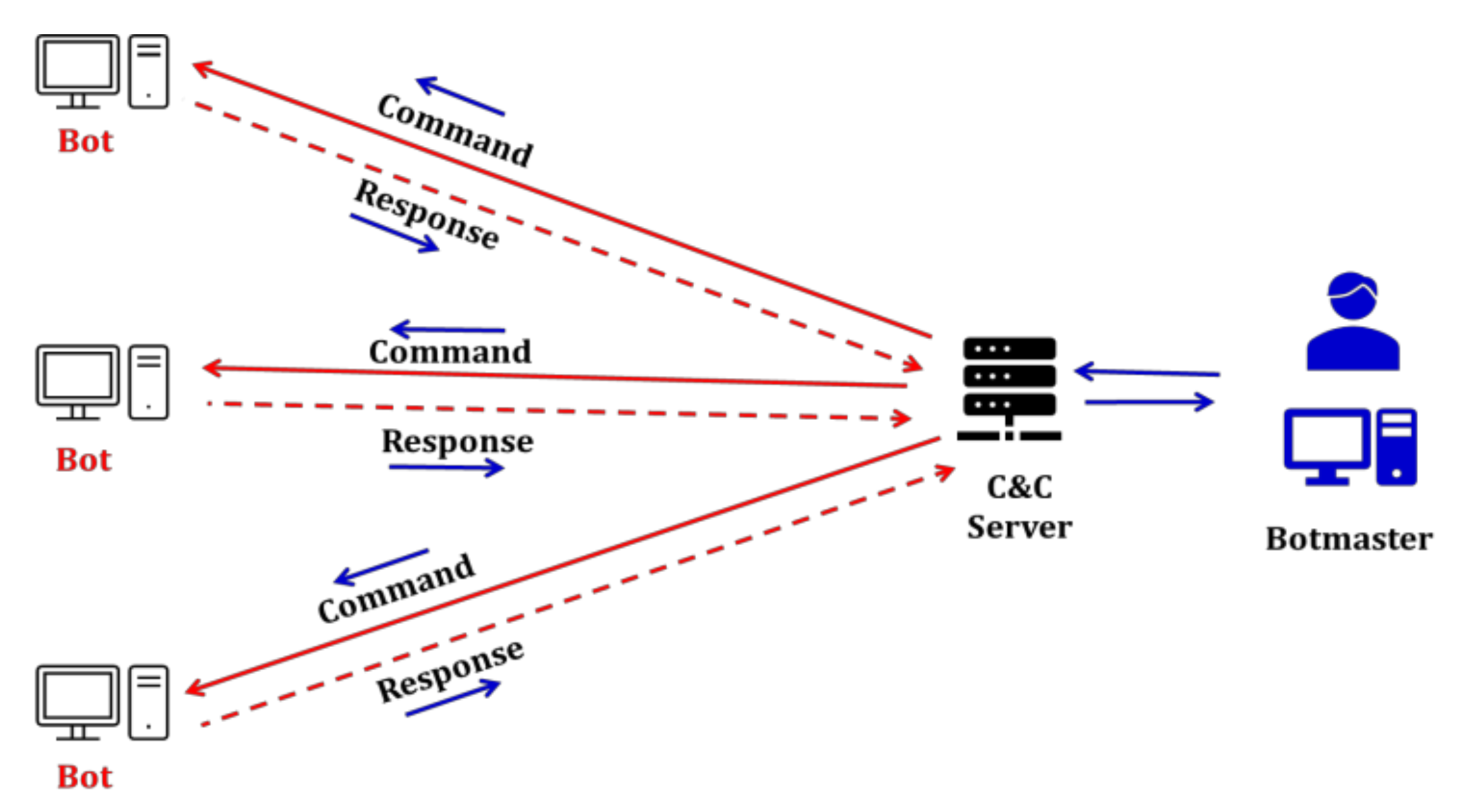
Diagram showing how scans from a Mirai botnet result in attempted

A hybrid method for analysis and detection of malicious executables in IoT network - ScienceDirect
Sensors, Free Full-Text
Advanced Malware Analysis Training Session 3 - Botnet Analysis Part 2
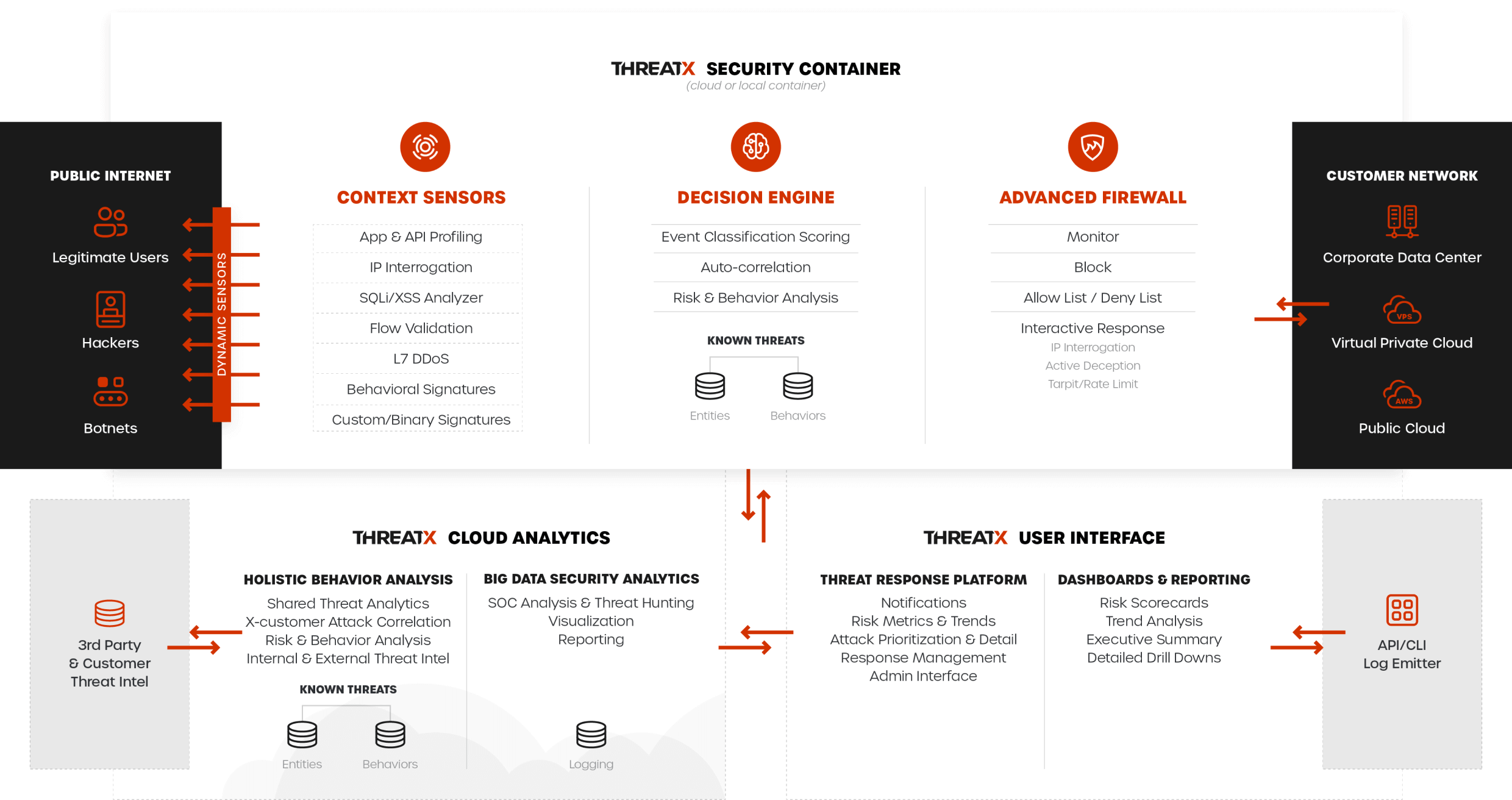
Introduction - ThreatX

Advanced Evasion Techniques - FasterCapital
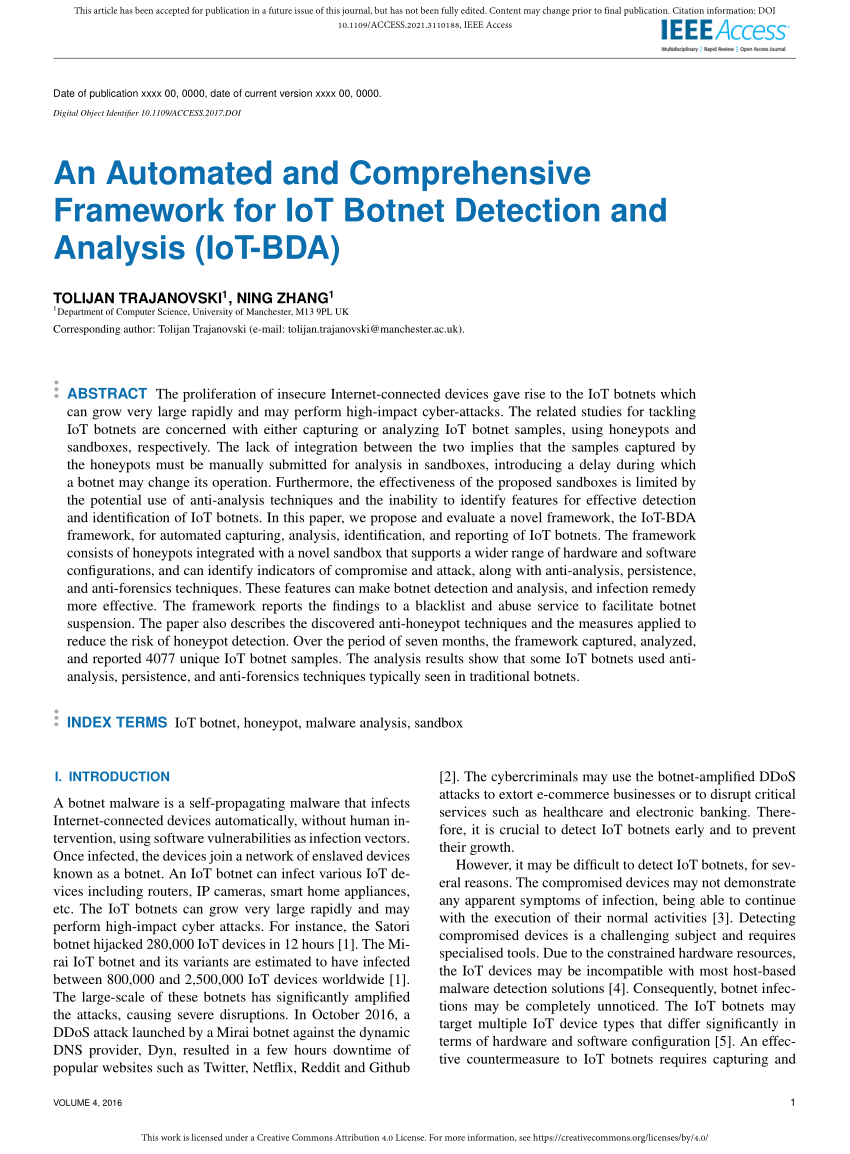
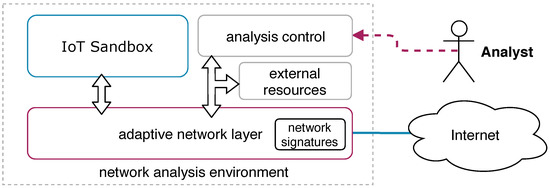
PDF) An Automated and Comprehensive Framework for IoT Botnet Detection and Analysis (IoT-BDA)
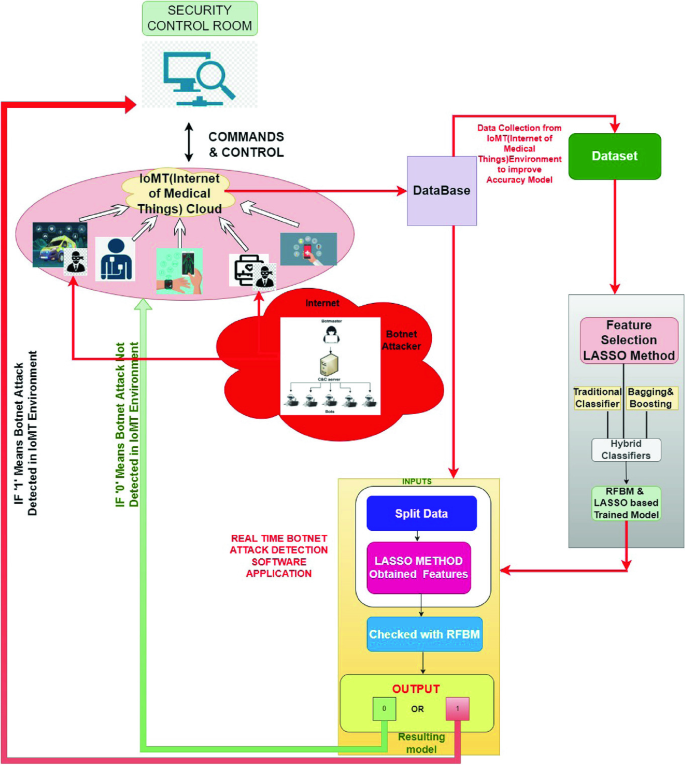
Botnet Attacks Detection Using Embedded Feature Selection Methods for Secure IOMT Environment

Ethical hacking for IoT: Security issues, challenges, solutions and recommendations - ScienceDirect

Adversaries' Evasions are Growing Faster than Defenders' Detections - Part 2
Into the Battlefield: A Security Guide to IoT Botnets - Security News
de
por adulto (o preço varia de acordo com o tamanho do grupo)