Indirect Command Execution – Penetration Testing Lab
Por um escritor misterioso
Descrição
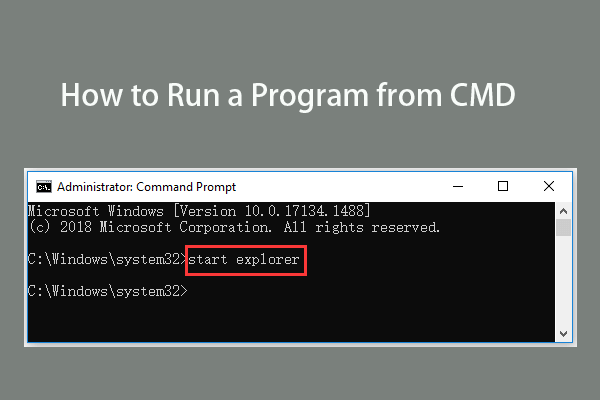
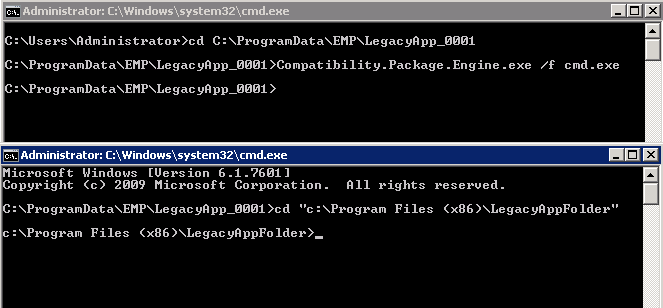
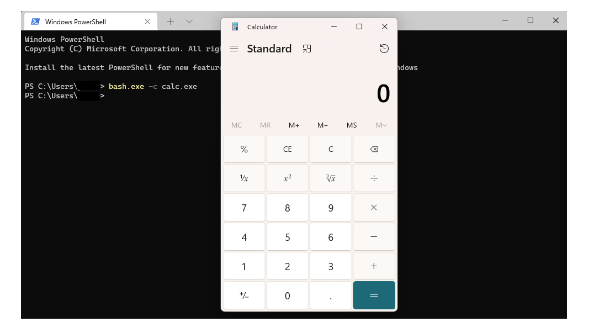
The windows ecosystem provides multiple binaries that could be used by adversaries to execute arbitrary commands that will evade detection especially in environments that are monitoring binaries such as "cmd.exe". In certain occasions the techniques described below could be used to bypass application whitelisting products if rules are not configured properly (whitelist by path or…

Branch predictor - Wikipedia

Exploring Prompt Injection Attacks, NCC Group Research Blog
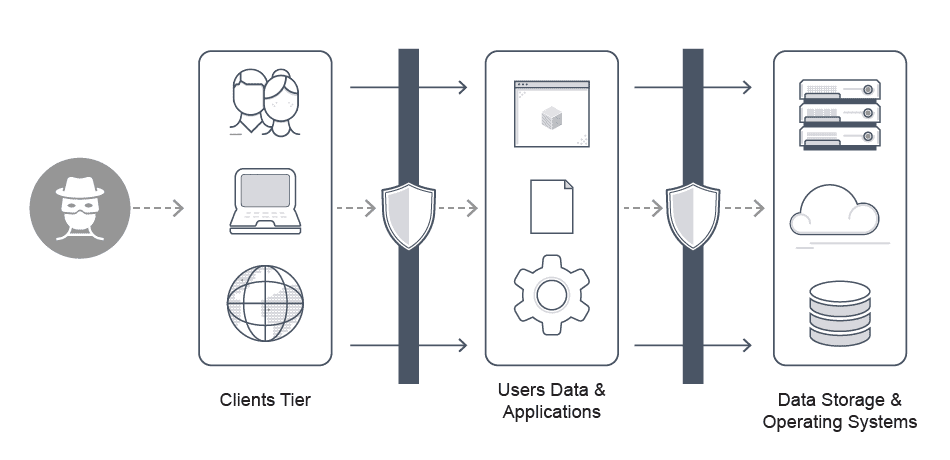
What is Application Security Architecture?

Security Testing: Types, Tools, and Best Practices
The Attack Path Management Manifesto, by Andy Robbins
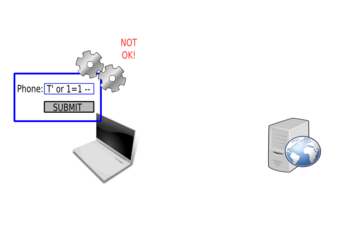
PentesterLab: Learn Web App Pentesting!

Kali Linux Web Penetration Testing Cookbook
TRY HACK ME: Living Off The Land Write-Up, by Shefali Kumari
PentesterLab: Learn Web App Pentesting!

Indirect Command Execution: Defense Evasion (T1202) - Hacking Articles

How prepared is the world? Identifying weaknesses in existing assessment frameworks for global health security through a One Health approach - The Lancet

Indirect Command Execution – Penetration Testing Lab

Indirect Command Execution: Defense Evasion (T1202) - Hacking Articles
de
por adulto (o preço varia de acordo com o tamanho do grupo)