The Hidden Threat to Your SecOps: Tampered Log Data
Por um escritor misterioso
Descrição
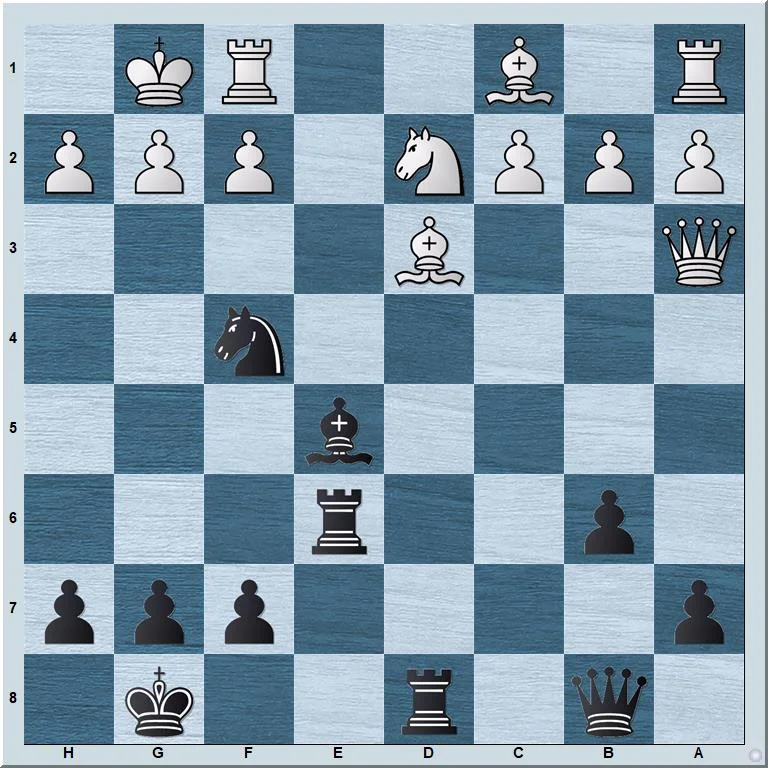
Log data plays a critical role in SecOps by providing insights into systems. This makes log data a popular target for cybercriminals.
Catch Me If You Can: A Rogue Cyber Security Professional, by Dennis Chow, The Startup
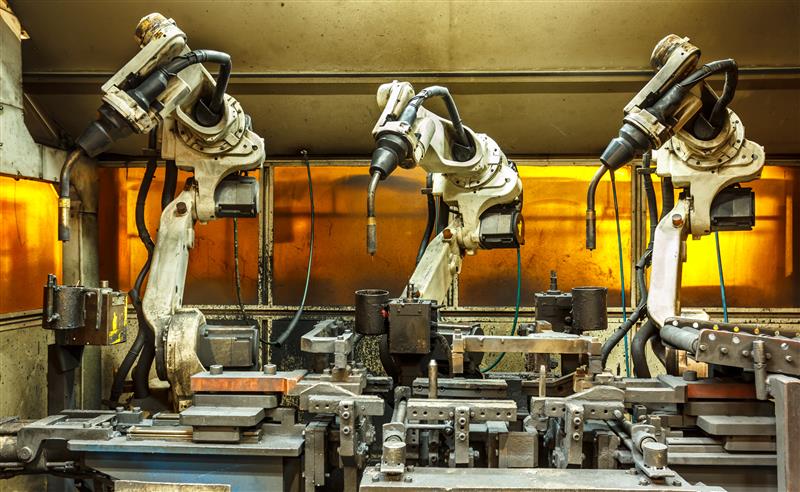
Unveiling the Hidden Risks of Industrial Automation Programming - Nachrichten zum Thema Sicherheit - Trend Micro DE

How to?! – ITSolutionDesign (Martin's technology notepad)
Threat-Hunting for Identity Threats in Snowflake
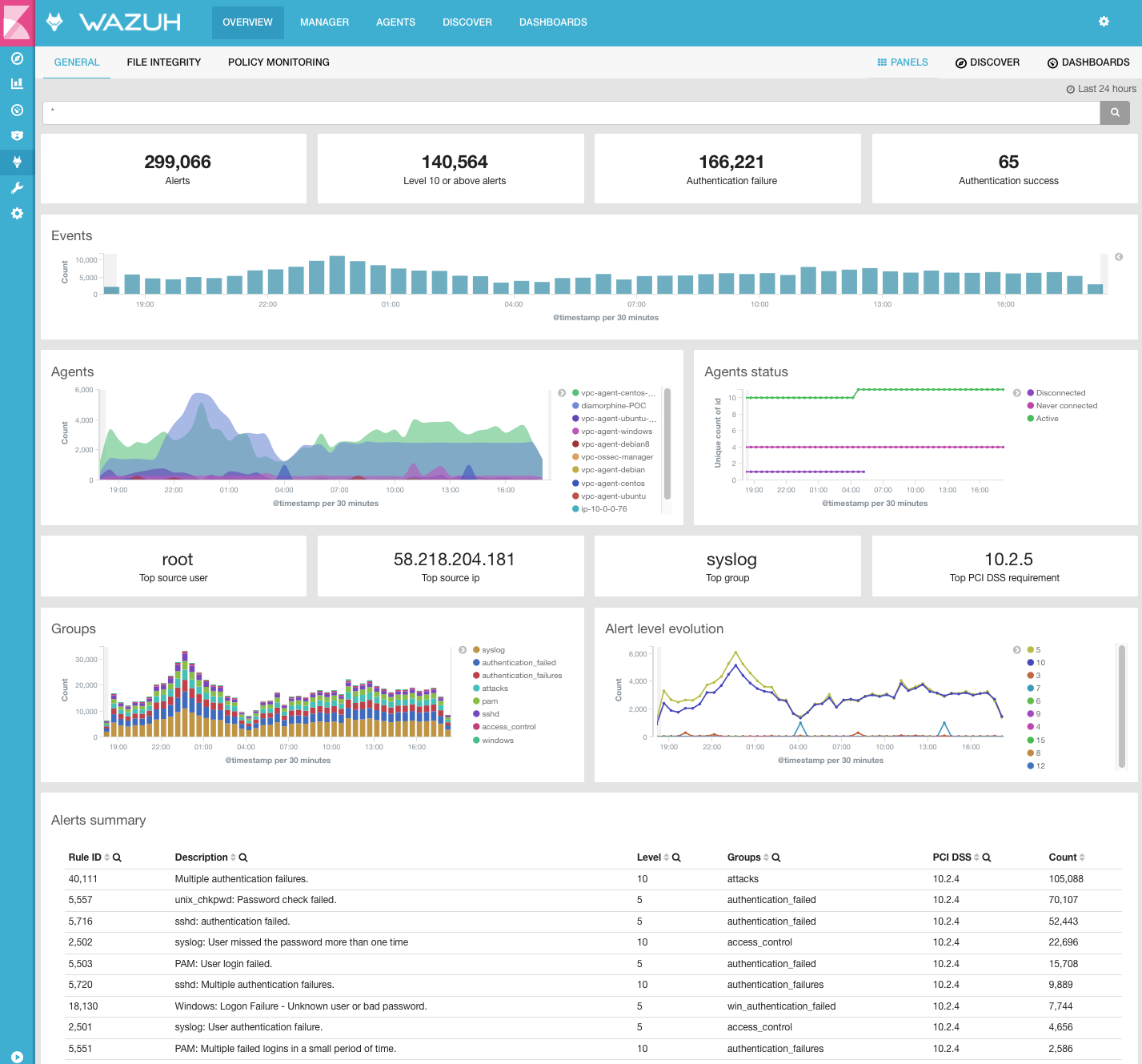
Top 5 open-source HIDS systems
How to configure Microsoft Defender for Endpoint

Brief: Threats from Retail Store-Based Intrusions

API Security: The Unbreakable Shield for Resilient Software
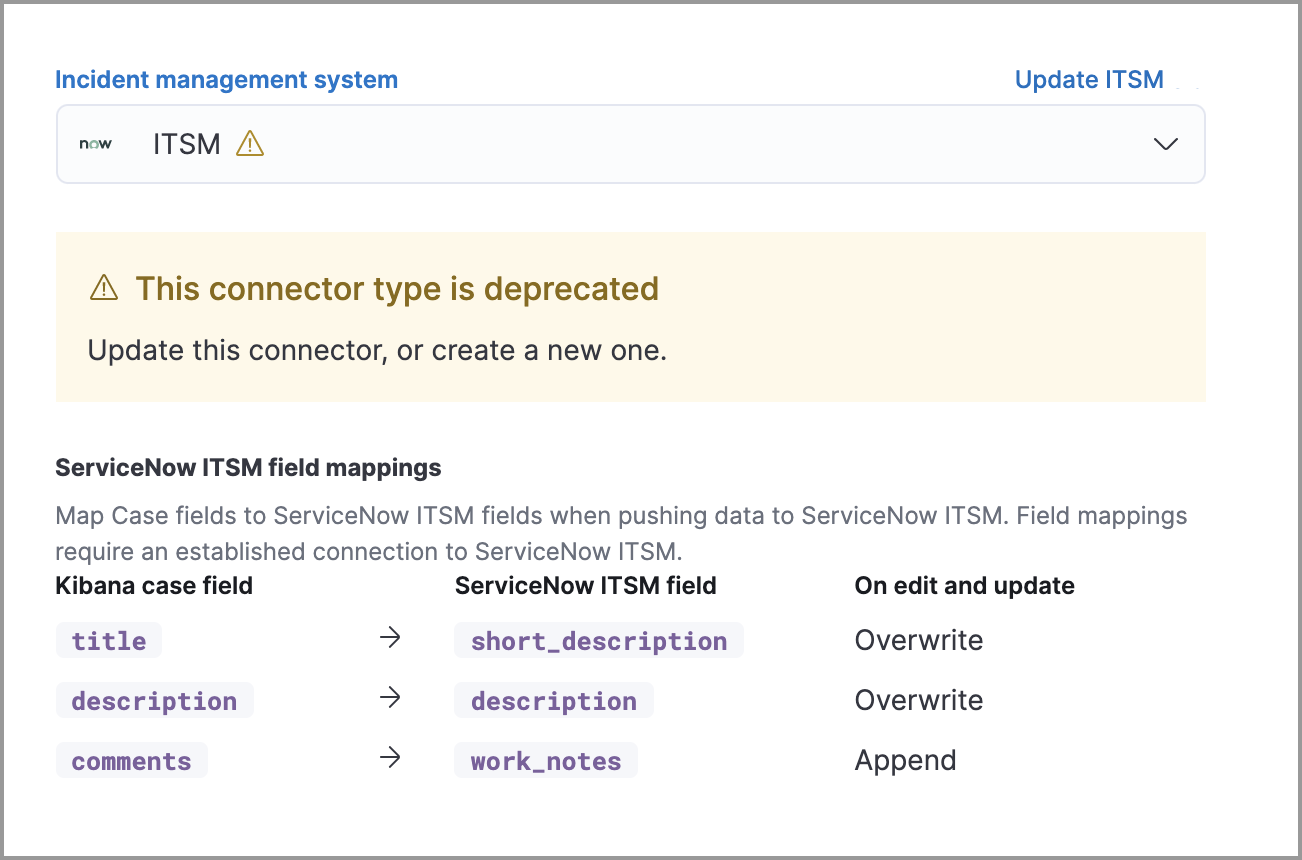
Update a deprecated ServiceNow connector, Elastic Security Solution [8.11]

Cyber Security Leading IT & Technology Recruitment Agency · Glocomms
.jpg)
Unveiling Unvalidated Redirects: The Hidden Web Security Threat

Cybersecurity Fundamentals - Attack Surfaces and Vulnerabilities - Orange Matter
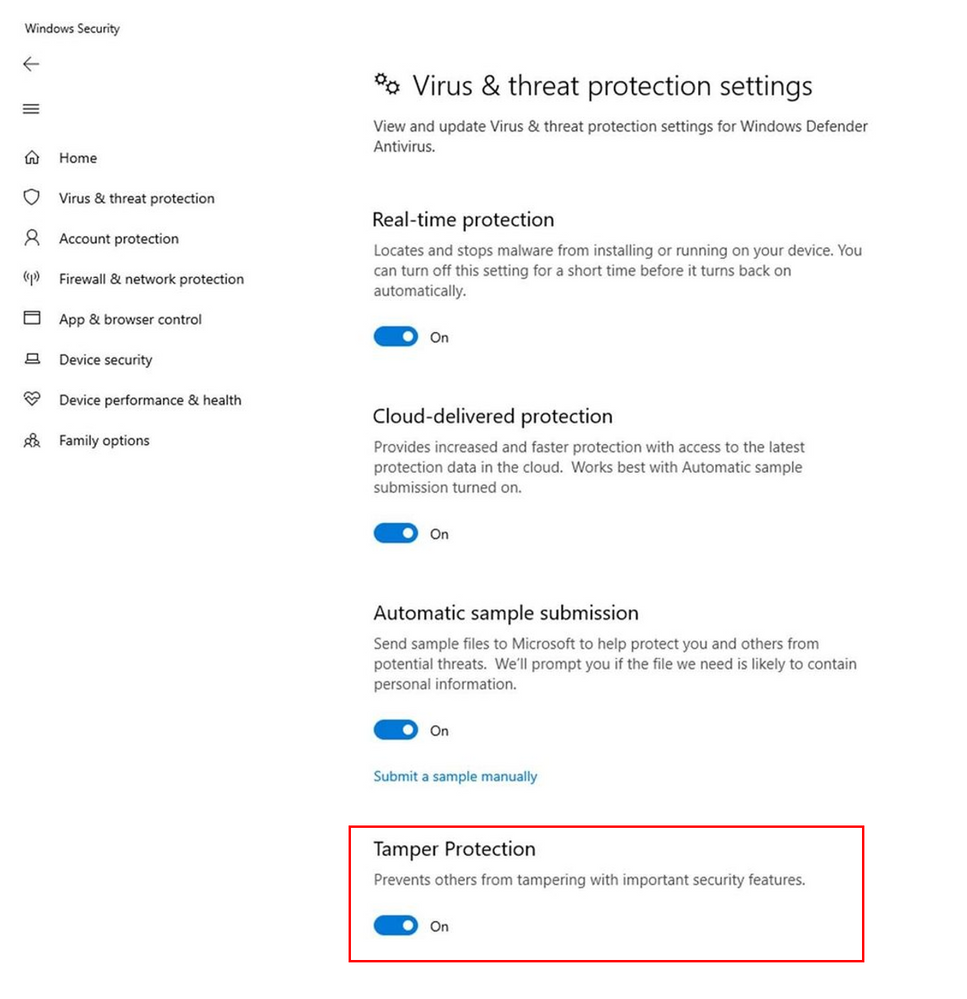
Tamper protection now generally available for Microsoft Defender ATP customers - Microsoft Community Hub

Courses for Security Core Concepts: Security Intermediate - Skillsoft
de
por adulto (o preço varia de acordo com o tamanho do grupo)