How hackers use idle scans in port scan attacks
Por um escritor misterioso
Descrição
Hackers employ a variety of port scan attacks to gain entry into an enterprise network. Idle scans are a popular method to mask the hacker
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.
Hackers exploit port scan attacks to mask their identities before launching an attack. One of their favorites: the idle scan.

A Complete Guide to Nmap, Nmap Tutorial
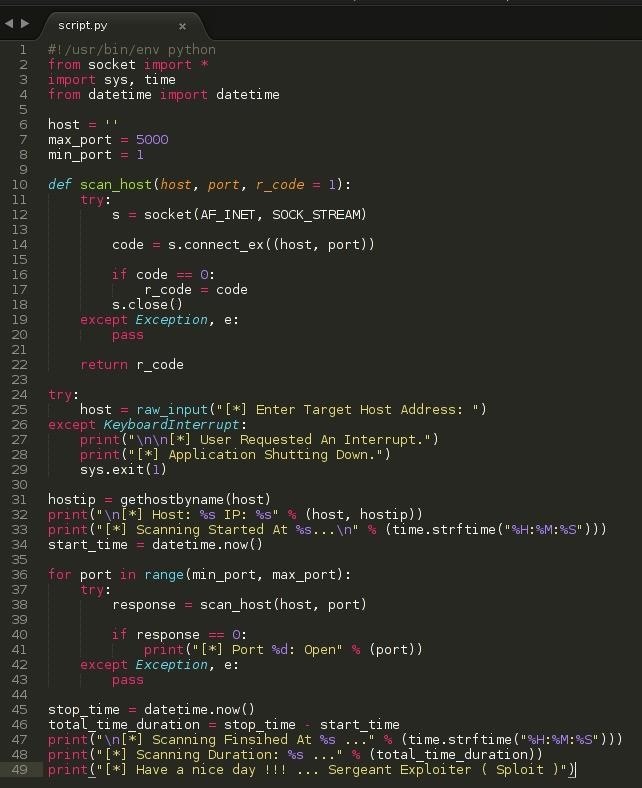
SPLOIT: How to Make a Python Port Scanner « Null Byte :: WonderHowTo

Nmap – How to Use Nmap – Spyboy blog
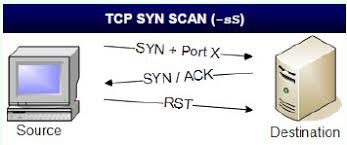
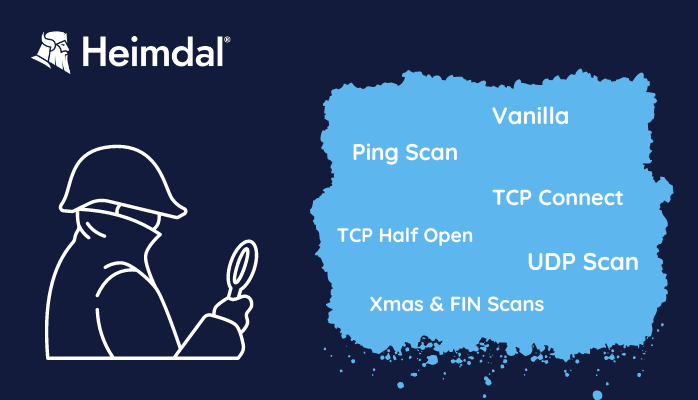
SYN Stealth, XMAS, NULL, IDLE, FIN
What Is a Port Scan Attack? Definition and Prevention Measures for Enterprises
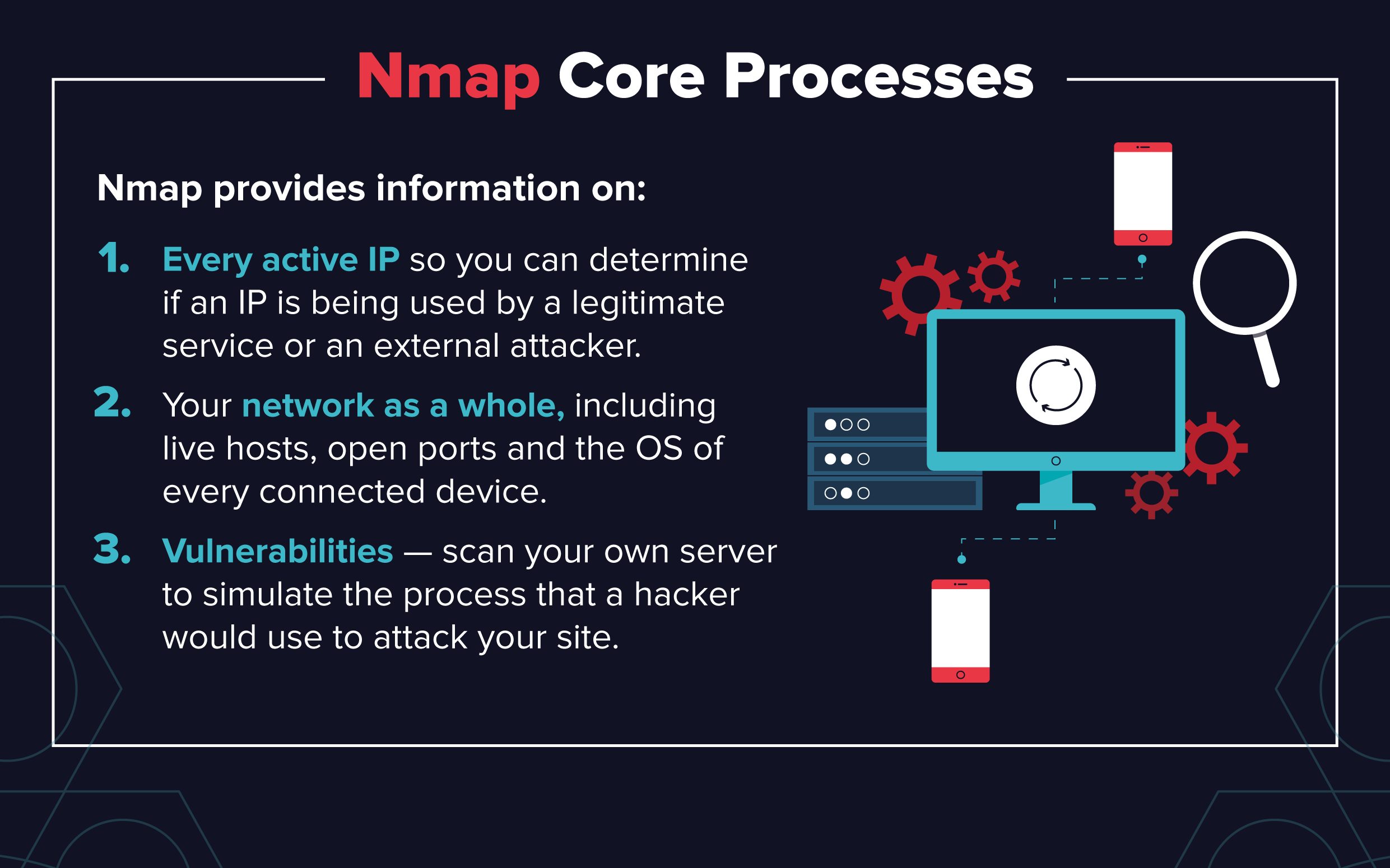
Essential Nmap Commands for System Admins - Penetration Testing Tools, ML and Linux Tutorials
A Complete Guide to Nmap, Nmap Tutorial

Ethical Hacking: Scanning Networks (2016) Online Class
Nmap cheat sheet: From discovery to exploits, part 2: Advance port scanning with Nmap and custom idle scan
Port Scanning based Attacks

Hacking techniques
de
por adulto (o preço varia de acordo com o tamanho do grupo)