Malware analysis Malicious
Por um escritor misterioso
Descrição

Overview of Malware Analysis and Detection

Malware Analysis: Steps & Examples - CrowdStrike
Highlight, take notes, and search in the book In this edition, page numbers are just like the physical edition

Practical Malware Analysis: The Hands-On Guide to Dissecting Malicious Software

A MS word malware analysis Part2: Analyzing malicious macros, by Nishan Maharjan

Malware Detection flowchart [64]

Malware Analysis - What is, Benefits & Types (Easily Explained)
11 Best Malware Analysis Tools and Their Features
What is Malware Detection? Why Malware Threat System?
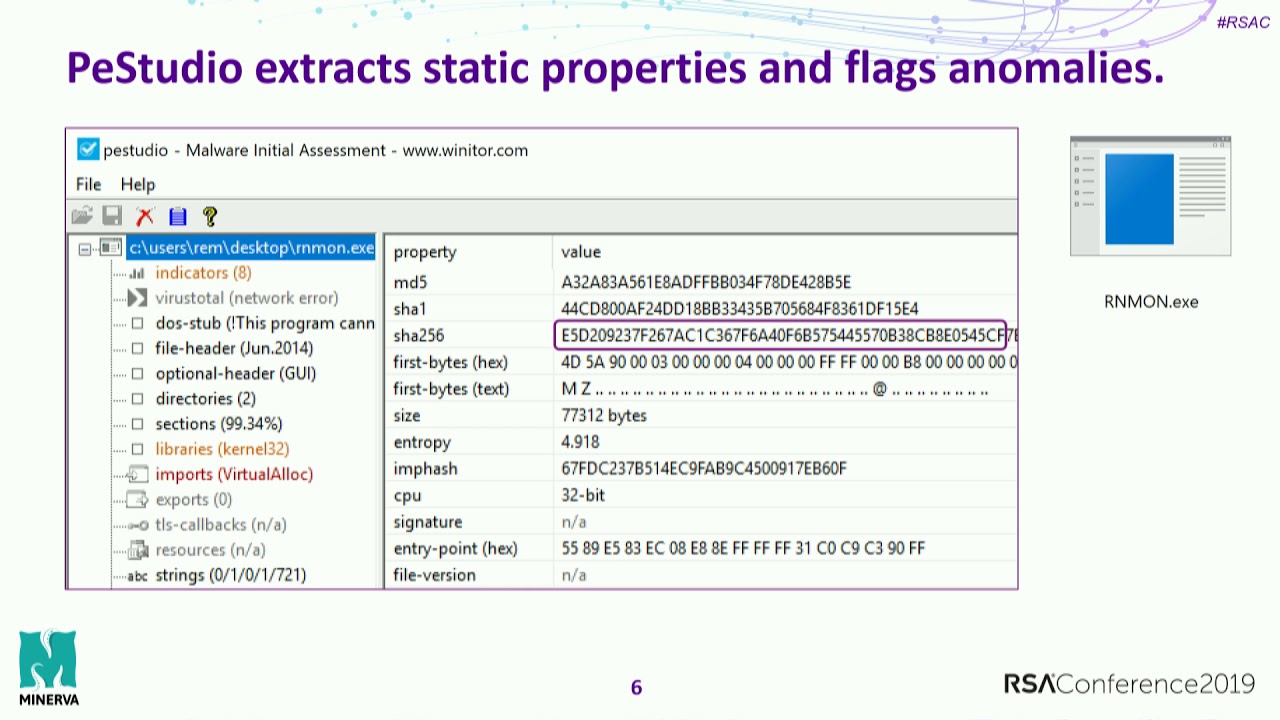
Practical Malware Analysis Essentials for Incident Responders
Highlight, take notes, and search in the book In this edition, page numbers are just like the physical edition

Malware Analyst's Cookbook and DVD: Tools and Techniques for Fighting Malicious Code
de
por adulto (o preço varia de acordo com o tamanho do grupo)