Malware analysis Malicious activity
Por um escritor misterioso
Descrição
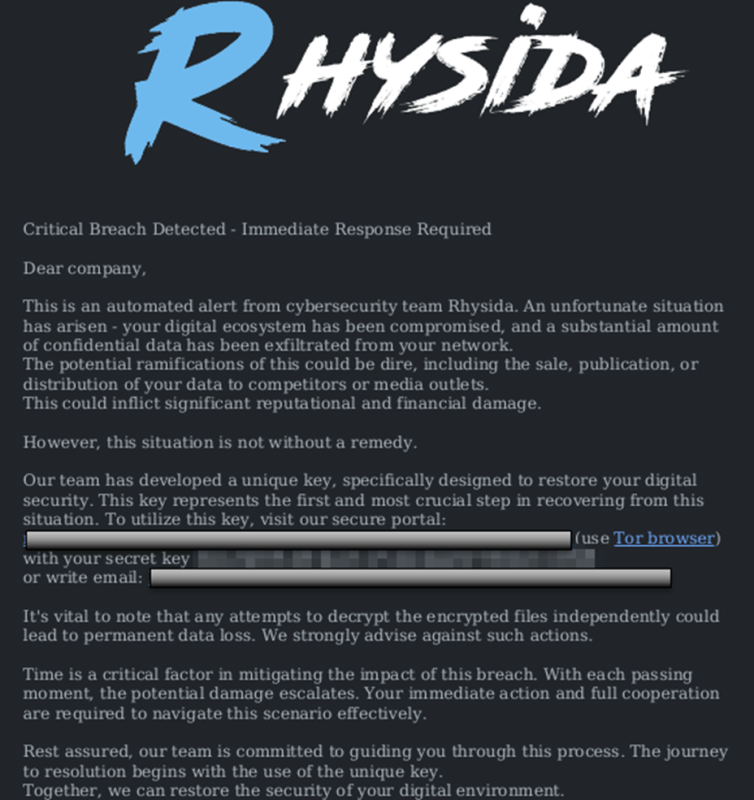
StopRansomware: Rhysida Ransomware

Feature Extraction and Detection of Malwares Using Machine

An Elastic approach to large-scale dynamic malware analysis

What is Malware? Definition, Types, Prevention - TechTarget
Download Free Antivirus Software

What is Malware? Definition, Types, Prevention - TechTarget

Routers Roasting on an Open Firewall: the KV-botnet Investigation
How to Analyze Malware's Network Traffic in A Sandbox

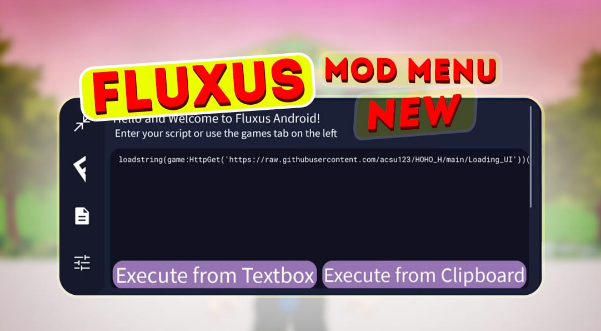
Malware analysis lockysample.bin.zip Malicious activity

Malware Analysis: Steps & Examples - CrowdStrike

Security Orchestration Use Case: Automating Malware Analysis
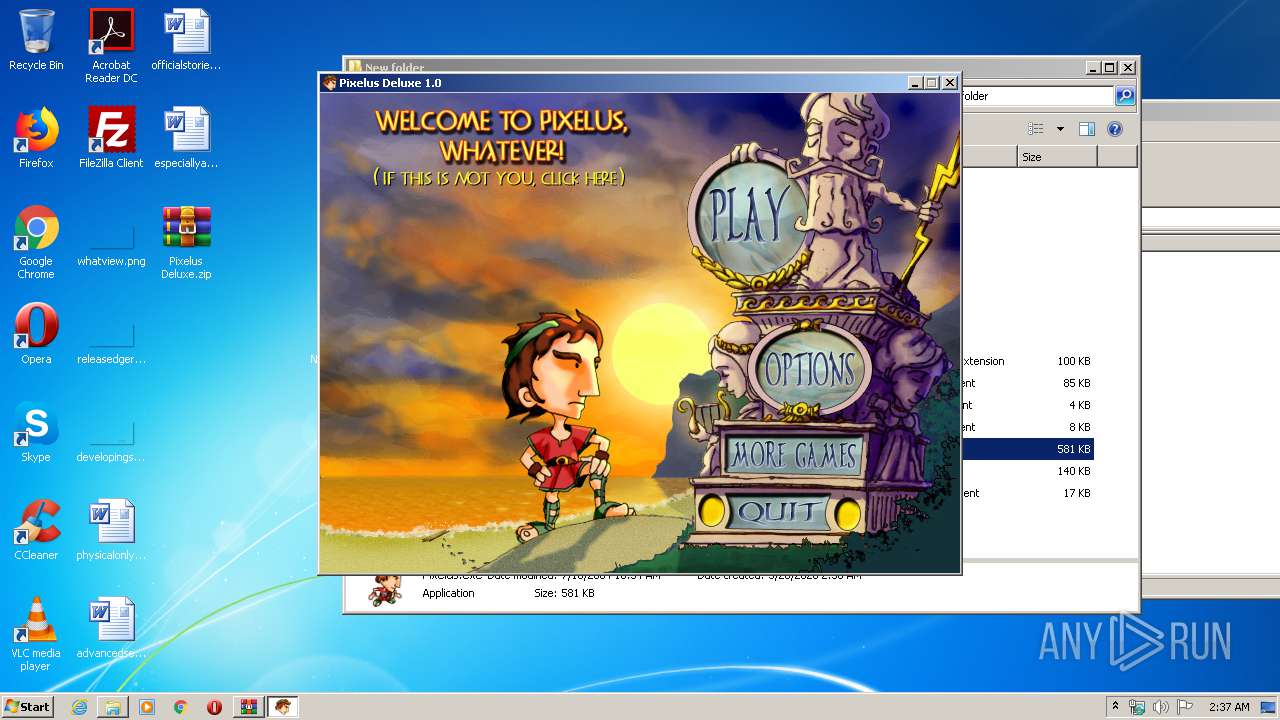
Malware analysis Pixelus Deluxe.zip Malicious activity

Malware Analysis: Steps & Examples - CrowdStrike
de
por adulto (o preço varia de acordo com o tamanho do grupo)