Malware analysis generator-no-survey-no-human-verification-2022-01-12 Malicious activity
Por um escritor misterioso
Descrição

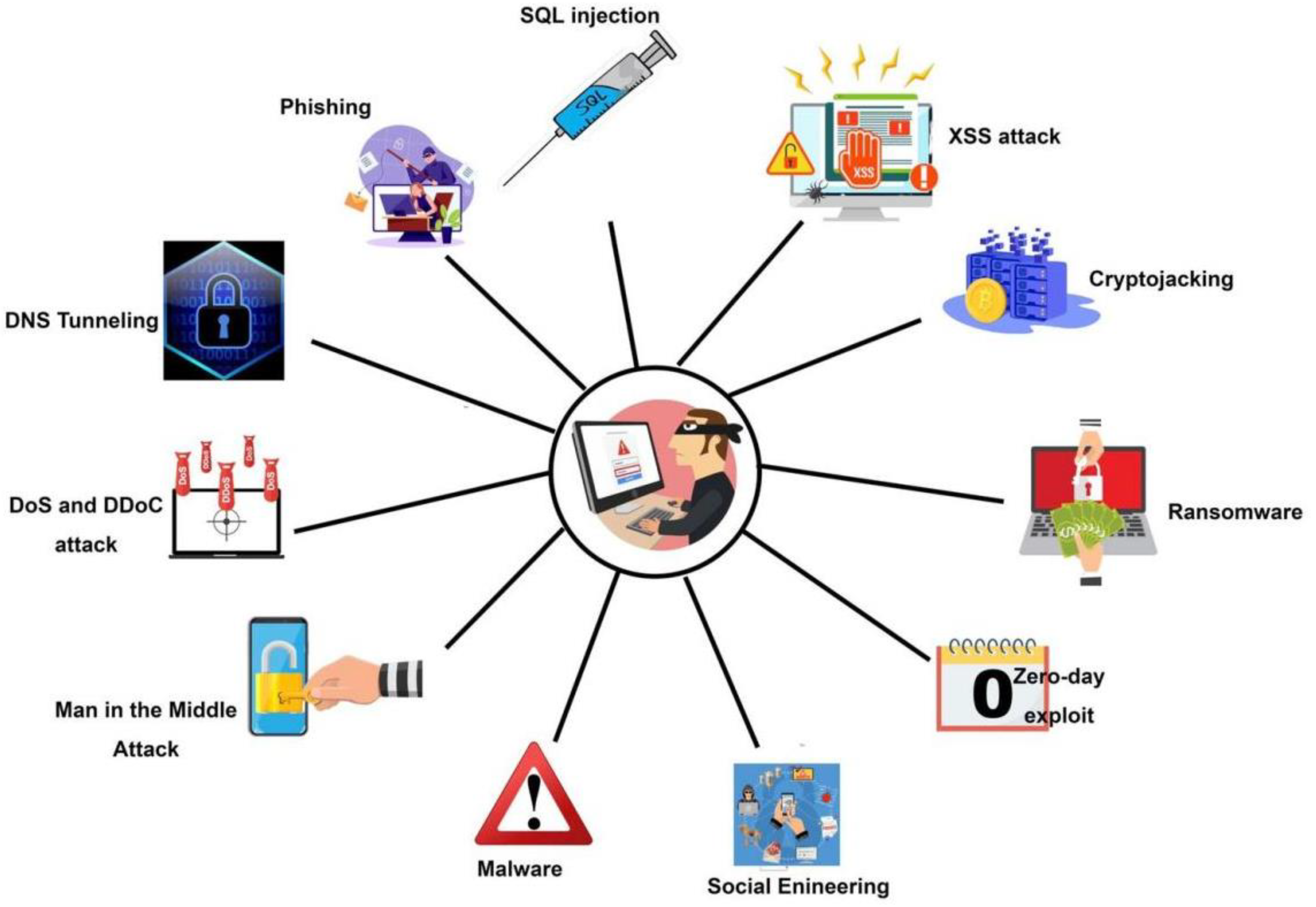
Exploring Prompt Injection Attacks, NCC Group Research Blog

A mining multitool - vulnerability database
Symmetry, Free Full-Text

Disarming visualization-based approaches in malware detection systems - ScienceDirect
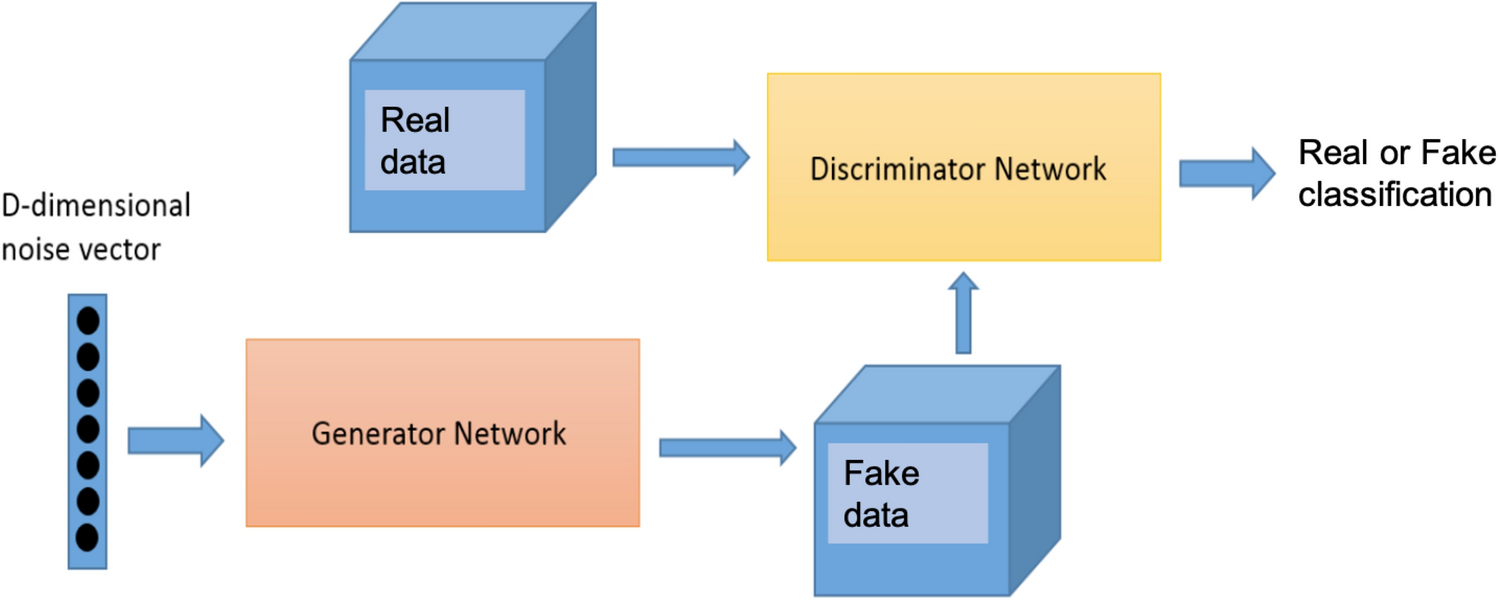
Synthetic flow-based cryptomining attack generation through Generative Adversarial Networks
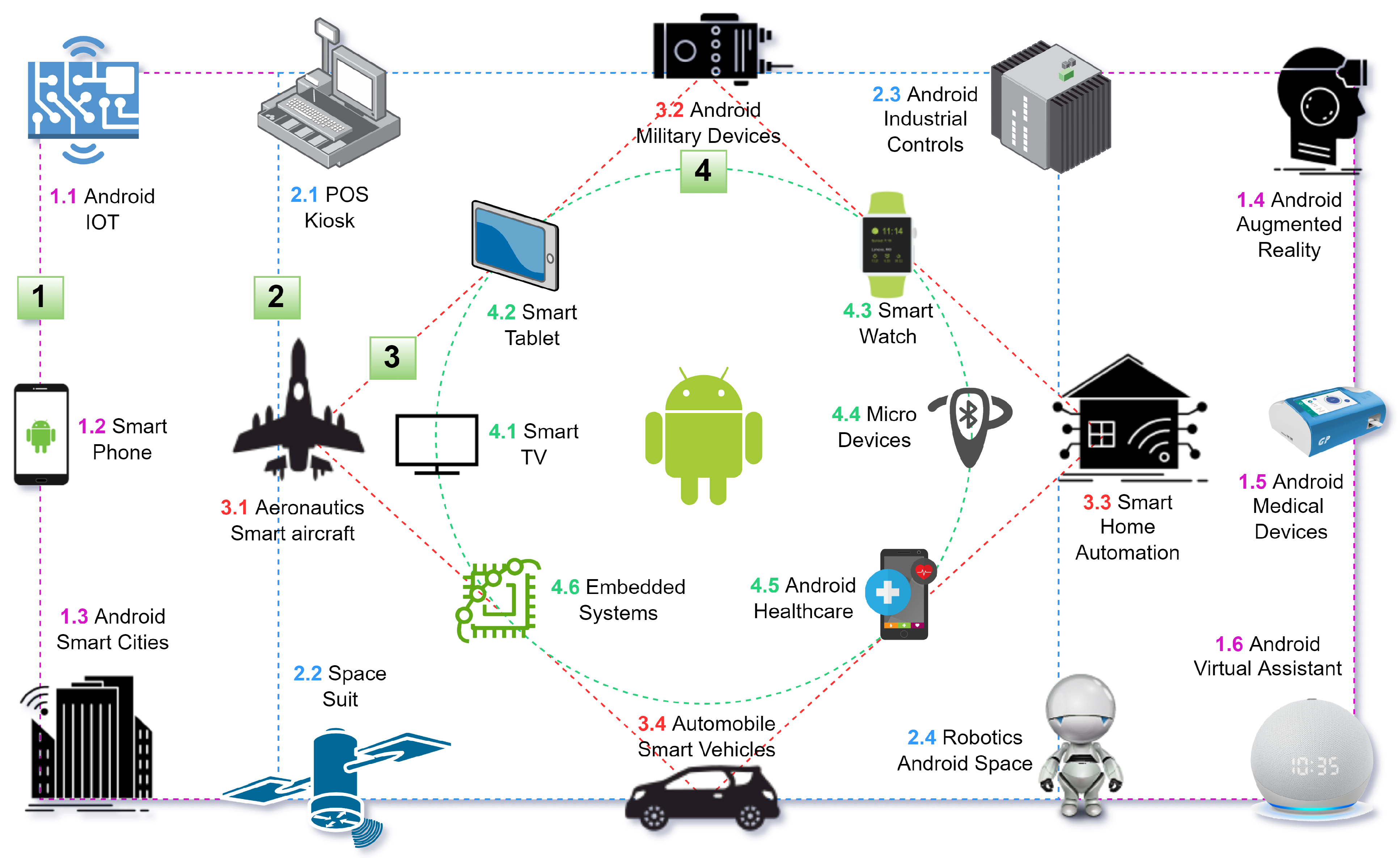
Technologies, Free Full-Text

Evolution toward intelligent communications: Impact of deep learning applications on the future of 6G technology - Abd Elaziz - WIREs Data Mining and Knowledge Discovery - Wiley Online Library

Explainable machine learning in cybersecurity: A survey - Yan - 2022 - International Journal of Intelligent Systems - Wiley Online Library
Malware analysis generator-no-survey-no-human-verification-2022-01-12 Malicious activity
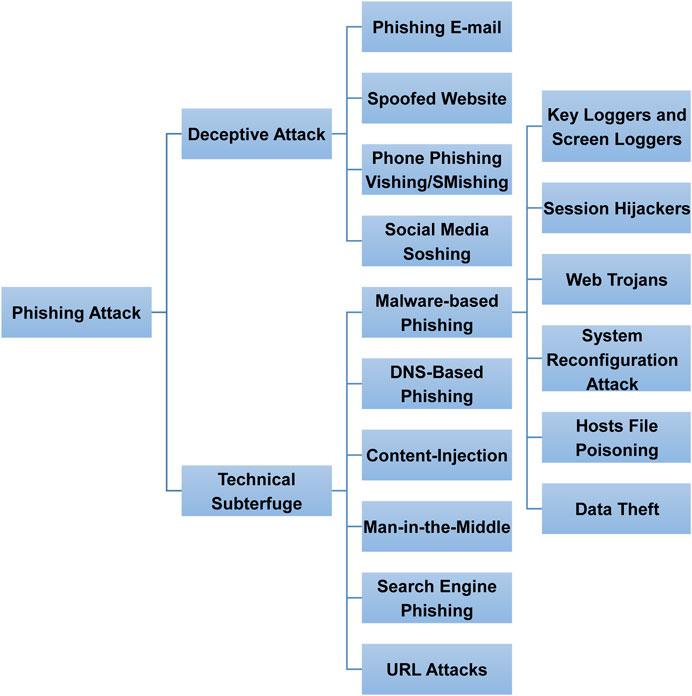
Frontiers Phishing Attacks: A Recent Comprehensive Study and a New Anatomy

Computer security - Wikipedia

424B4
Dave Greenfield, Author at Cato Networks
de
por adulto (o preço varia de acordo com o tamanho do grupo)