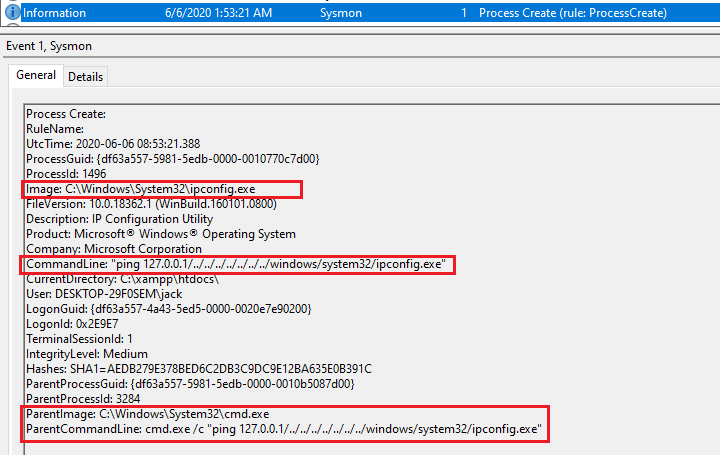
Cmd Hijack - a command/argument confusion with path traversal in cmd.exe
Por um escritor misterioso
Descrição
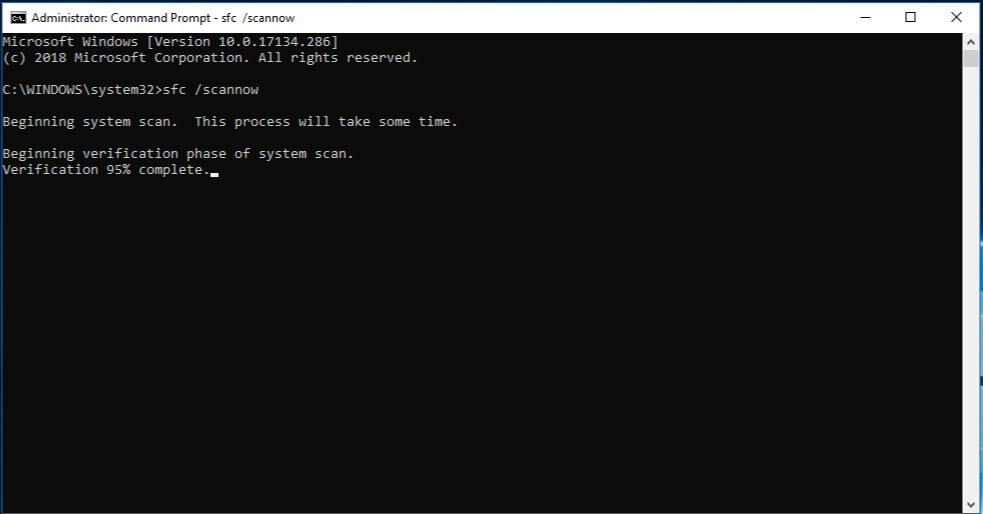
This one is about an interesting behavior 🤭 I identified in cmd.exe in result of many weeks of intermittent (private time, every now and then) research in pursuit of some new OS Command Injection attack vectors.
So I was mostly trying to:
* find an encoding missmatch between some command check/sanitization code and the rest of the program, allowing to smuggle the ASCII version of the existing command separators in the second byte of a wide char (for a moment I believed I had it in the StripQ

ExploitWareLabs - Cmd.exe Hijack - a command/argument
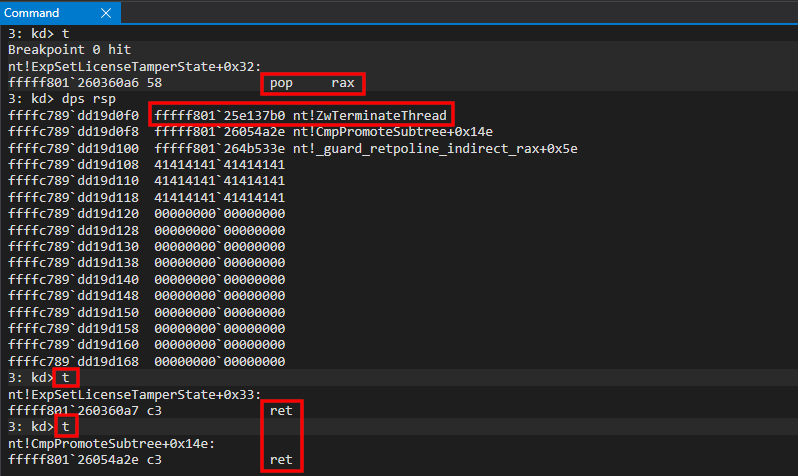
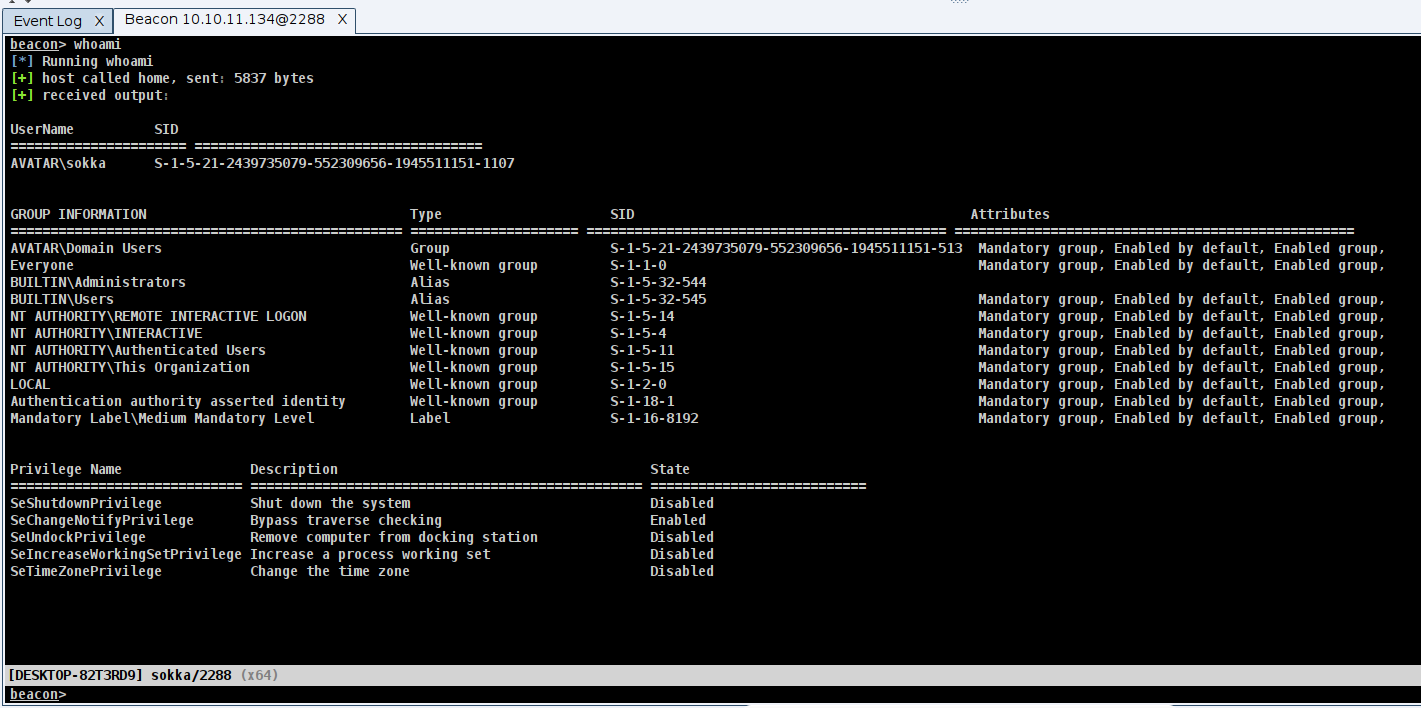
Exploit Development: No Code Execution? No Problem! Living The Age of VBS, HVCI, and Kernel CFG

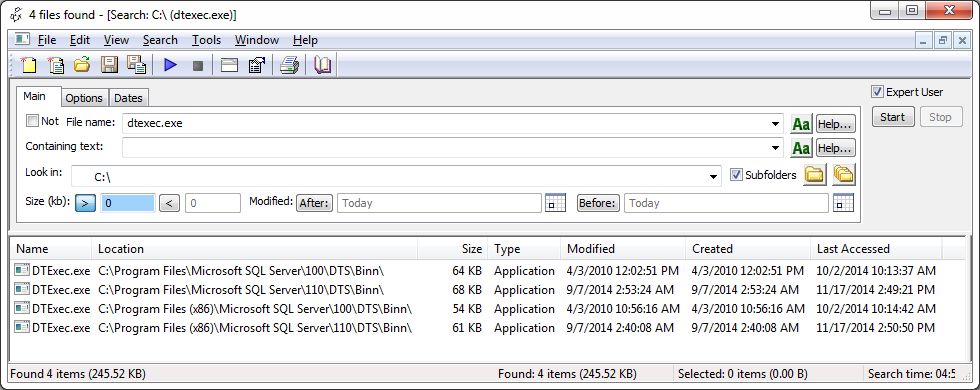
How to pass parameter to cmd.exe and get the result back into C# Windows application - Stack Overflow
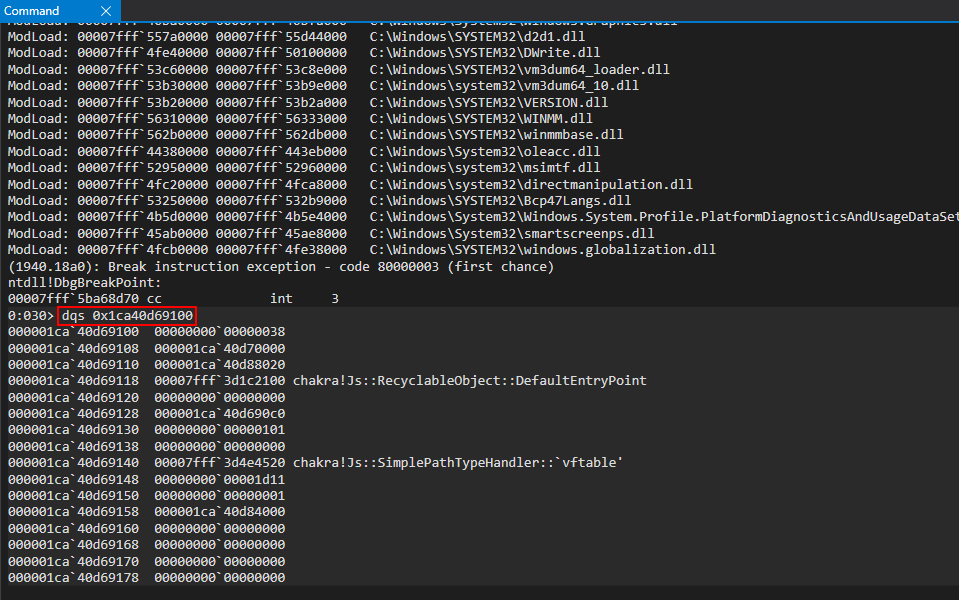
Exploit Development: Browser Exploitation on Windows - CVE-2019-0567, A Microsoft Edge Type Confusion Vulnerability (Part 3)

Curso Metasploit - Part. 2.2 - Comandos de metasploit
Process Injection Part 1: The Theory - Secarma: Penetration Testing and Cybersecurity Company

Cmd Hijack - a command/argument confusion with path traversal in cmd.exe : r/netsec
How to handle CMD start with '&' in the command path with Windows 10 (windows, command line, command-line arguments, escape characters, admin) - Quora

What is the best way to hack using cmd? - Quora
running a cmd within powershell - Microsoft Q&A

Cmd hijack vulnerability - Vulnerabilities - Acunetix

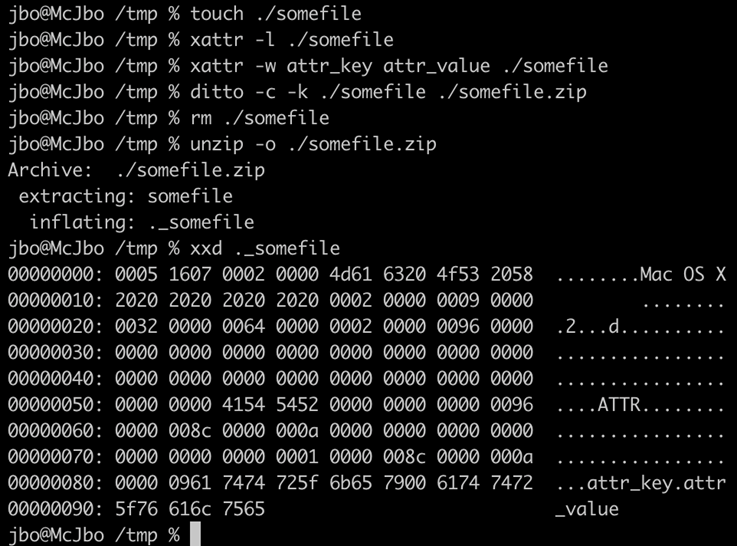
Orchestration of APT malware evasive manoeuvers employed for eluding anti-virus and sandbox defense - ScienceDirect
Cmd Hijack - a command/argument confusion with path traversal in cmd.exe
Swedish Windows Security User Group » Microsoft security intelligence
de
por adulto (o preço varia de acordo com o tamanho do grupo)